Microsoft’s Basic Authentication (sometimes known as Legacy Authentication) protocols are being permanently disabled for Exchange Online in October of 2022. An alternative to basic authentication should be in place before protocols are deprecated to avoid any widespread impacts on operating systems and applications currently using them. Here, you’ll find information on why Microsoft’s basic authentication protocols are being disabled and our recommendations for mitigation.
What is basic authentication?
Basic authentication is a simple authentication method where credentials (typically a username and password) are sent automatically along with every request to verify it. This is the traditional authentication method users are familiar with. Basic authentication protocols have been disabled on new tenants since 2018. They were phased out on new operating systems (OS’) in the same year.
Do I have Microsoft’s basic authentication?
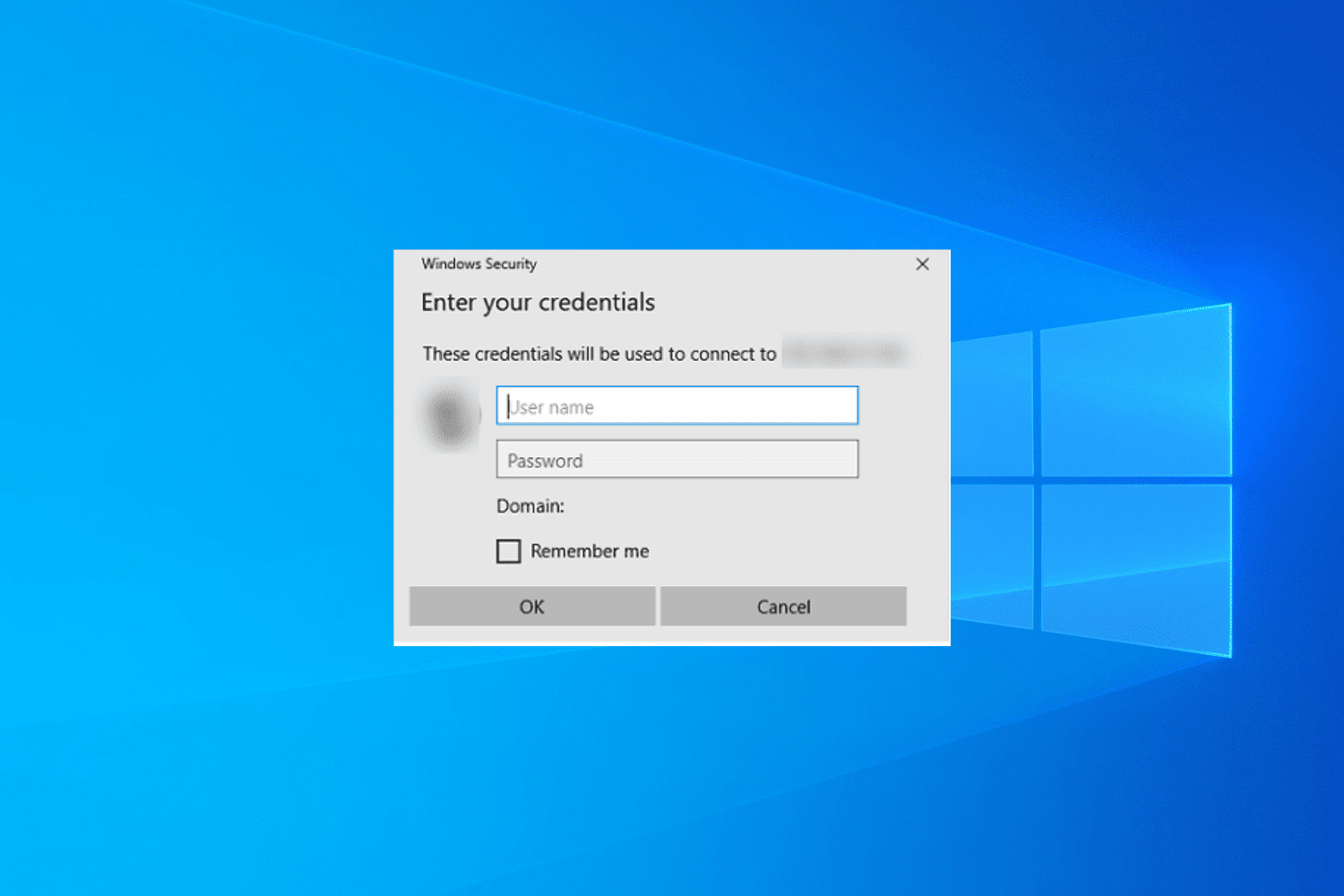
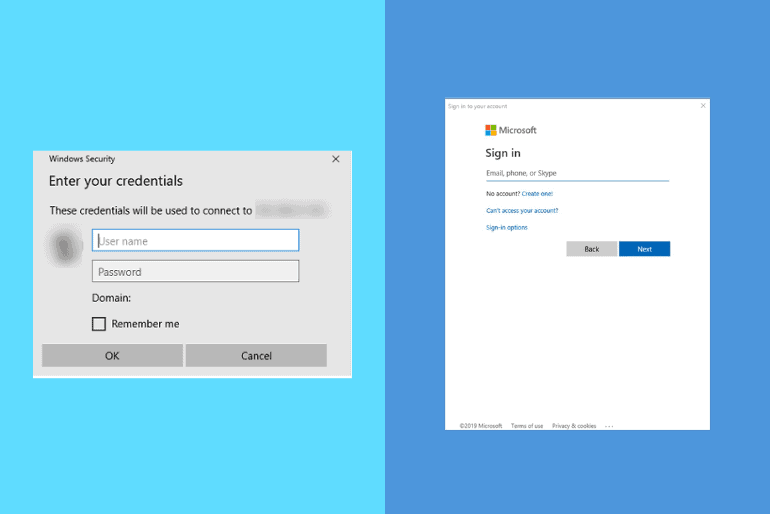
There are a few ways to determine whether your organization is currently using basic authentication protocols. One of the easiest ways is to look at how you login. If you’re seeing a popup dialog box rather than a browser page, chances are it’s basic authentication.
A Risk Assessment can help you run scripts or audit your systems to see if basic authentication is being leveraged. Tools including Microsoft’s Admin Center, Message Center, and Azure Sign-on log can also be reviewed to determine where basic authentication is still in use.
Why is Microsoft’s basic authentication being disabled?
According to Microsoft, it’s not only outdated – it’s unsafe. To improve security, Microsoft is requiring applications to use modern authentication (OAuth 2.0 token-based authorization), which eliminates reusing tokens. SMTP authentication will still be available – for now.
This authentication method often stores credentials locally, which can cause unintended security risks. If systems are compromised, credentials could be stolen and used to access other endpoints. Due to this, basic authentication is not only outdated – it can pose a security threat to your business.
Protocols enabled this way can be used to bypass multifactor authentication (MFA). Unless the protocols are fully disabled, an attacker could use them to bypass the MFA requirement for O365 – even if you’re using third-party MFA.
What happens when basic authentication is disabled?
If you have legacy systems or applications relying on this method of authentication, simply put – they will break. Line of Business (LOB) applications, email, scanners, etc. could all stop working. This could have a widespread impact to your organization. It’s important to take preventative measures to keep these issues from occurring.
ADNET’s recommendation
There are several options for organizations still leveraging basic authentication for Microsoft Exchange Online. Our recommendation is to use one of these mitigation techniques rather than opting out entirely. While opting-out is an option, it should be a last resort.
- Review the aforementioned areas to identify where basic authentication may be used in your organization.
- Perform upgrades. Many clients and applications can be updated to leverage modern authentication (OAuth 2.0).
- Implement workarounds. For many use cases of basic authentication, there may be other ways to achieve desired outcomes such as leveraging other technologies or changing processes.
- Apply for an “opt-out” exception with Microsoft: As a last resort exceptions can be applied for prior to September 1st, 2022.
ADNET often discovers basic authentication being used through the audits performed during Risk Assessments. If you don’t have a Risk Assessment scheduled prior to October 2022, ADNET suggests reviewing your Azure logs to see what’s currently using basic authentication and coming up with a plan to ensure a seamless transition. If you’d like assistance, don’t hesitate to reach out to us – we’re here to help!
